OSINT Technologies to Detect Terrorist Actions
In December 2025, two gunmen, “motivated by ISIS,”[1] opened fire on a “Chanukah by the Sea” celebration at Sydney’s Bondi Beach. Fifteen people were killed and at least 40 more injured.[2] This act of terrorism joins a growing list of attacks that have seared global memory. In New York, the September 11 terrorist attacks killed nearly 3,000 people.[3] In Paris, roughly 130 people died and more than 400 were injured when suicide bombers and others attacked theatres, restaurants, and the Stade de France.[4]
Less often remembered are the smaller acts of terrorism that occur more frequently across the globe. In 2023, a single Tunisian National Guard member opened fire at a pilgrimage to the El Ghriba Synagogue in Djerba, killing five people.[5] Later that same year, a terrorist murdered one man and injured two others in a knife-and-hammer assault near the Eiffel Tower.[5] In two separate occurrences on London Bridge, terrorists stabbed 10 people to death.[6]
Terrorism — ideologically or politically motivated acts of violence perpetrated against non-combatants — takes two forms: coordinated attacks committed by organized cells, networks, or groups; and smaller attacks typically committed by “lone wolf” terrorists. Preventing terrorism depends on analysts’ abilities to spot and stop both types of actors before the violence starts. AI-powered systems for strategic threat intelligence and identity risk intelligence can help.
Learn the basics
Video
Using Babel Street OSINT Tools to Prevent Terrorist Attacks

Use Case
Using Babel Street to Automate and Improve Intelligence Operations
How Babel Street can help accelerate intelligence operations

Blog
How Can Cyber Threat Intelligence Help Protect Critical Infrastructure
Cyberattacks on critical infrastructure have become increasingly frequent and sophisticated. These attacks can have devastating consequences, disrupting essenti...
Investigating terrorism by type
Combatting terrorism is a complex, multi-pronged effort, typically involving strategies and tactics coordinated by a variety of government agencies. These agencies strive for national collaboration, and to share intelligence with similar agencies operating in their ally countries across the globe.
Programs run the gamut from traditional investigations and physical surveillance (such as CCTV monitoring) to community engagement. In virtually all cases, digital intelligence is a vital component of counterterrorism efforts. Investigative agencies monitor the internet, particularly social media, and dark web forums, to track the communications and activities of suspected terrorists.
What are they looking for? What are the signs of a potential terrorist at work?
The answer is: It depends. Organized terrorist groups and lone wolves use the internet in different ways.

Penetrating organized terrorist groups
Organized terrorist networks, cells, and groups use social media platforms and dark web forums for the dissemination of propaganda, for planning, and for general communications.
Take Hamas as an example. Hamas is a political/military organization governing the Gaza Strip. Many nations[7] consider Hamas a terrorist organization. Hamas uses popular messaging apps to communicate. Some of its channels have contained calls to action for hundreds of thousands of user members.[8]
But for Hamas and similar organizations, online communications cannot replace real-world recruitment, radicalization, and training.
To bolster their numbers, members of organized terrorist organizations engage in face-to-face recruitment of friends, family, and neighbors. They exploit potential recruits’ existing political and religious views and grievances. They target the disenfranchised — including young people and people suffering from poor mental health — with promises of comradeship. They imbue potential recruits with a sense of purpose.
Recruits typically become members though a radicalization process that occurs in real-world locales. Hamburg’s Blue Mosque is one example. In 2023, Germany’s Federal Administrative court upheld a ruling that the mosque operates as a “extremist Islamic organization” pursuing “anti-constitutional objectives.”[9] At the mosque and similar sites worldwide, recruits are subject to intensive ideological education. Camps and safehouses provide physical space for training in weapons, explosives, and guerrilla warfare. Larger terrorist groups typically have an almost martial chain of command, and, as members rise through the ranks, they learn how to plan and execute terrorist acts.[10]
Online communications and recruiting activities constitute only one part of an organized network’s recruitment and training strategy. And because law enforcement now so closely monitors suspected terrorist sites in the physical world, counterterrorism organizations believe that organized groups’ reliance on the internet will only grow.

Tracking lone wolves
Lone wolves typically don’t use the internet as part of a broader terror strategy. Rather, the digital arena may provide these terrorists with their sole connection to the extremist ideologies of like-minded people. And this connection need not be “live:” While chatroom interactions certainly inspire would-be lone-wolf terrorists, so do static encounters such as reading extremist blogs or watching terrorist videos.
“Lone wolves” are defined as one or two terrorists working without the assistance of an organized terrorist network. They often prove hard for law enforcement to spot.

Why?
Counterterrorism professionals monitor known terrorist locales — physical and virtual. In Germany, they watch the Blue Mosque. In the United States, they can follow the comings and goings at known militia compounds: Elohim City in Oklahoma, the Bundy Ranch in Nevada, the Aryan Nations Compound in Idaho.[11] Online, investigators monitor chat sites and dark web forums where members of organized terrorist groups congregate.
But a lone wolf typically has no physical location to visit, no organized group to exchange instant messages with, no elders to consult. He may independently decide, as one terrorist did, to strap on an automatic rifle and shoot up a Washington, D.C. pizzeria to save the non-existent victims of a fictious child sex-tracking ring while simultaneously exposing the political leaders he believed to be running the organization.[12]
It is important to note that while lone wolves may have no direct contact with organized terrorist networks, organized terrorist groups regularly institute one-way communications with the public. They do this to create lone wolves dedicated to terrorist causes.[13] Terrorists believe that if you produce enough propaganda, you’ll convert someone to your cause. Emerging AI technologies help in these communications. Increasingly, terrorist organizations use generative AI to create propaganda, amplify their presence on social media, and create deepfakes in support of their causes.

In addition to merely inspiring would-be lone-wolf terrorists, the internet provides them with information needed to commit their crimes. In the past, a terrorist may have wanted to blow up a public space, but have no idea how to do so. Today, The Anarchist’s Cookbook is available as a free PDF download. Anyone can search the internet for instructions on “how to build a bomb,” buy precursor chemicals online, and purchase illegal weapons on the dark web.
Lone-wolf terrorism now “poses a serious emerging threat to the United States.”[14] How serious? Consider this. In many cases, lone wolves become lone wolves because they are too radical for more established anti-government or terrorist populations.[15] Oklahoma City bomber Timothy McVeigh is an example. He considered joining a private paramilitary organization opposing what it viewed as overreach by the United States government. McVeigh reportedly found the group insufficiently radical and quit after only a few meetings.[16]
Why Babel Street?
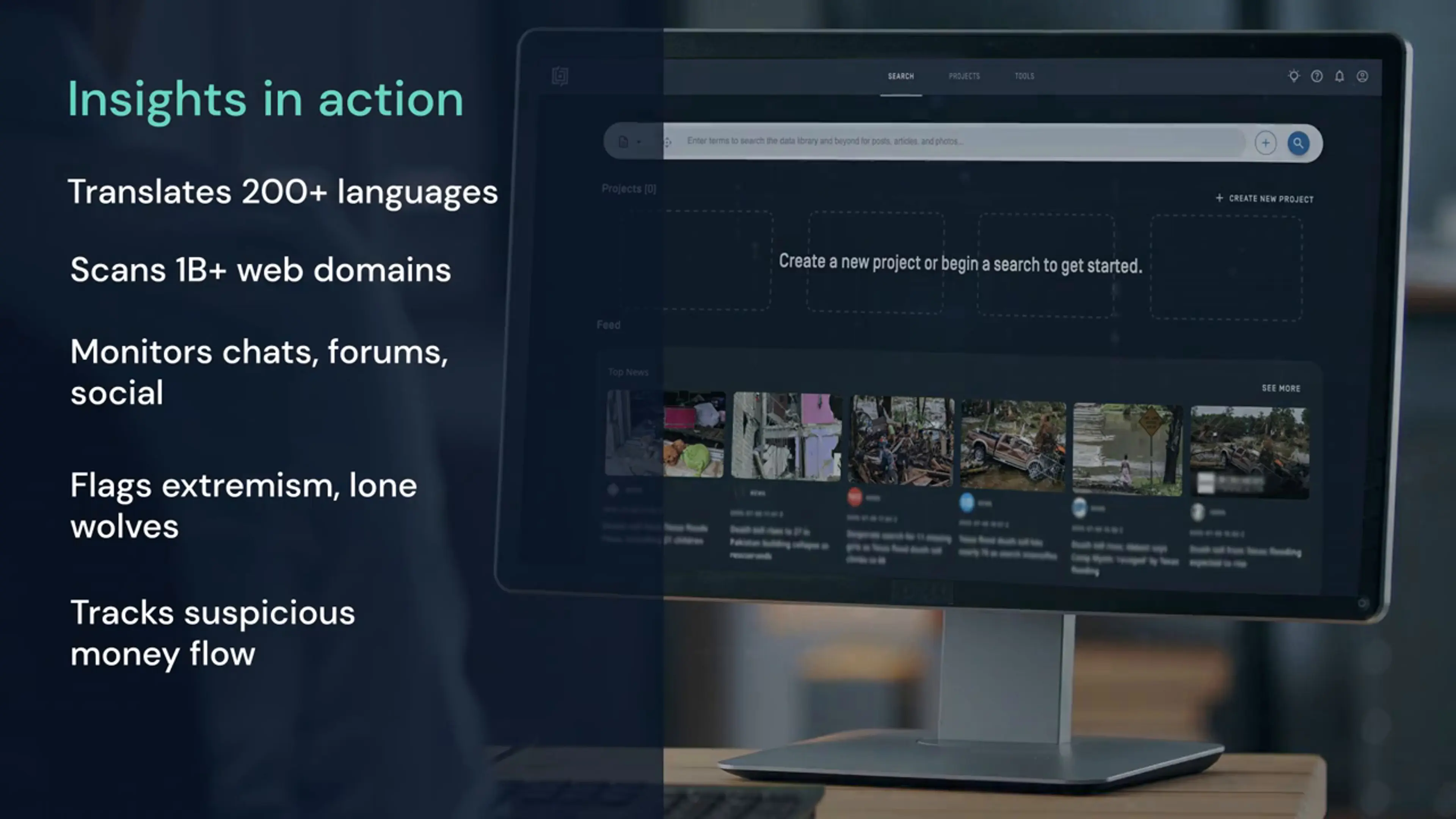
Delivering mission-grade risk intelligence quickly and at scale, Babel Street sets a new standard for counterterrorism investigations. Our solution provides persistent searches of a vast array of publicly and commercially available information sources (PAI/CAI). These include more than a billion top-level domains; real-world interactions generated on chats, social media posts, online comments, and message boards; government and academic information; news sources, and more. Babel Street understands more than 200 languages (including Arabic, Chinese, Russian, and other languages rendered in non-Latin scripts), and translates information into the user’s language of choice.
These capabilities help counterterrorism professionals:
Detect extremism and stem recruitment
Babel Street continuously monitors social media sites and the dark web for signs of recruiting activity. The platform rapidly detects evidence of recruitment campaigns — including distorted narratives, deepfakes, and bot amplification. Natural language processing capabilities reveal influence operations unfolding across social media sites worldwide, while algorithms extract signs of extremism percolating in written materials, videos, chat communities, and technical forums. Using Babl Street, counterterrorism analysts can pinpoint influence cells that are manipulating perceptions and conversations. With this information in hand, they can mobilize targeted counter-messaging.
Analyze terrorist networks
Babel Street can help unravel terrorist networks, cells, and groups. Our solution extracts terrorism clues from online communications. Understanding standard languages, regional dialects, slang, and emojis, Babel Street detects coded language, threats, and other terrorism indicators.
In addition, Babel Street can help map relationships among terrorists and those they try to recruit. Babel Street charts key connections among people, locations, and events by examining hundreds or thousands of associations within a specific social network or discussion group, uncovering previously unknown or hidden relationships, and identifying those participants who wield the most influence. Visualizations of these relationships are also provided. Once influencers are identified, Babel Street empowers users to delve deeper into those influencers’ online profiles, activities, and associates.
Dismantle terror plots
Much as Babel Street can help spot radicalization efforts, it also empowers analysts to find and dismantle terrorism plots. Managed attribution capabilities help counterterrorism professionals infiltrate dark web forums, chatrooms, and other sites where terrorists gather. There, they can anonymously uncover coalescing threats — pinpointing extremists discussing potential targets, weapons sourcing, maneuvers, and vulnerabilities. Using this insight, counterterrorism professionals can counter or halt these activities.
Track and stem the flow of money
Organized networks, cells, and groups need cash for major, coordinated acts of terror. According to the U.S. Department of the Treasury’s latest report on terrorist financing,[17] they have no problem asking for it. “The most common financial connections between individuals in the United States and foreign terrorist groups entail individuals directly soliciting funds for, or attempting to send funds to, foreign terrorist groups utilizing cash, registered money services, [and] businesses” the report says. Terrorists and their sympathizers solicit funds from “witting and unwitting donors worldwide.”[18] Here again, new technologies bolster terrorists’ efforts. Increasingly, they use virtual assets, blockchain, and crowdfunding platforms to solicit funds.
Babel Street can help spot these solicitations when they are instituted or conducted via social media, in chatrooms, or on the dark web. With this visibility, government agencies can take appropriate action. In addition, Babel Street anti-money laundering solutions are already in use at financial institutions worldwide, helping them better comply with AML mandates. In doing so, Babel Street helps to significantly reduce instances of terrorist financing.
Spot lone wolves
The capabilities discussed above can also help spot lone wolves. Babel Street helps counterterrorism professionals find and react to lone wolves’ online activities. Babel Street helps investigators see lone wolves as they:
- Enter chat rooms devoted to fringe or terrorist causes
- Create social media platform pages dedicated to their beliefs
- Post videos
- Blog
- Write manifestos, and publish them online
- Publicly discuss their travel to red-flag countries
- Openly complain about their expulsion from organized radical or extremist groups
All these activities may signify future terrorist action.
Spotting and stopping terrorists — whether organized cells or lone wolves — is vital to ensuring the safety of nations and individuals worldwide. By delivering advanced risk intelligence solutions, Babel Street can help the counterterrorism cause.
You might also like

Data Sheet
Secure Access for Intelligence Operations
How Babel Street Secure Access managed attribution solution protects intelligence agents during online investigations.

Data Sheet
Babel Street Insights Synthesis
The benefits and features of Synthesis for enhanced social network and relationship mapping

Data Sheet
Babel Street Insights
Product brief highlighting benefits and features of Babel Street Insights for People Search, Document Search, and maximizing the use of publicly available information.

Blog
Social Media Threat Monitoring and Sentiment Analysis Improves National Security
A foreign company advertises on Facebook, targeting impoverished people in your country with offers of suspiciously well-paying agricultural jobs or domestic po...
End Notes
1. Blinken, Antony J., “Press Statement: 22nd Anniversary of the September 11, 2001 Attacks,” United States Department of State, September 2023, https://www.state.gov/22nd-anniversary-of-the-september-11-2001-attacks/#:~:text=On%20September%2011%2C%202001%2C%20terrorists,homeland%20in%20our%20nation's%20history
2. Wikipedia, “Mumbai Attacks,” accessed July 2024, https://en.wikipedia.org/wiki/2008_Mumbai_attacks
3. Wikipedia, “November 2015 Paris Attacks,” accessed July 2024, https://en.wikipedia.org/wiki/November_2015_Paris_attacks
4. Ministère De L’Europe Et Des Affaires Ètrangères, “Tunisia – Attack in Djerba,” accessed July 2024, https://www.diplomatie.gouv.fr/en/country-files/tunisia/news/article/tunisia-attack-in-djerba-10-05-23
5. BBC, “Paris attack near Eiffel Tower leaves one dead and two injured,” December 2023, https://www.bbc.com/news/world-europe-67604591
6. BBC, “London Bridge: What we know about the attack,” December 2019, https://www.bbc.com/news/uk-50594810
7. Wikipedia, “Hamas,” accessed July 2024, https://en.wikipedia.org/wiki/Hamas#:~:text=Argentina%2C%20Australia%2C%20Canada%2C%20Israel,to%20condemn%20Hamas%20was%20rejected
8. Allyn, Bobby, “The Telegram app has been a key platform for Hamas. Now it's being restricted there,” NPR, October 2023, https://www.npr.org/2023/10/31/1208800238/the-telegram-app-has-been-a-key-platform-for-hamas-now-its-being-restricted-ther#:~:text=Now%20it's%20being%20restricted%20there,-October%2031%2C%202023&text=Matt%20Slocum%2FAP-,Telegram%20has%20removed%20popular%20Hamas%2Dlinked%20accounts%20from%20the%20messaging,to%20take%20down%20the%20channels.
9. VOA News, “German Court Categorizes Islamic Center as ‘Extremist Islamic Organization’,” July 2023, https://www.voanews.com/a/german-court-categorizes-islamic-center-as-extremist-islamic-organization-/7163231.html
10. Simon, Jeffrey D., “Lone Wolf Terrorism,” Prometheus Books, 2013
11. Ibid
12. Wikipedia, “Pizzagate conspiracy theory,” accessed July, 2024, https://en.wikipedia.org/wiki/Pizzagate_conspiracy_theory
13. Simon, Jeffrey D., “Lone Wolf Terrorism,” Prometheus Books, 2013
14. Ahmed, Saeed, “Who were Syed Rizwan Farook and Tashfeen Malik?” CNN, December 2015, https://www.cnn.com/2015/12/03/us/syed-farook-tashfeen-malik-mass-shooting-profile/index.html
15. Simon, Jeffrey D., “Lone Wolf Terrorism,” Prometheus Books, 2013
16. Ibid
17. Ridley, Gary, “Michigan Militia still active 20 years after Oklahoma City bombing,” Michigan Live, April 2015, https://www.mlive.com/news/flint/2015/04/militias_remains_active_20_yea.html
18. U.S. Department of the Treasury, “2024 National Strategy for Combating Terrorist and Other Illicit Financing,” May 2024, https://home.treasury.gov/system/files/136/2024-Illicit-Finance-Strategy.pdf
19. Ibid
Disclaimer:
All names, companies, and incidents portrayed in this document are fictitious. No identification with actual persons (living or deceased), places, companies, and products are intended or should be inferred.